In today’s digital economy, organizations rely heavily on interconnected systems, cloud infrastructure, remote work environments, and data-driven decision-making. While these advancements drive innovation and efficiency, they also introduce a broader and more complex attack surface. Cyber threats have evolved beyond isolated incidents—they now target entire enterprise ecosystems.
This is where Enterprise Cyber Security Architecture becomes essential. It serves as the strategic blueprint that ensures security is not just an afterthought but an integral part of an organization’s technology framework. For businesses navigating digital transformation, a well-designed cybersecurity architecture helps align technology, security controls, and compliance practices to create a resilient and secure operational environment.
Organizations across industries are increasingly turning to experienced cybersecurity consulting firms like Illume Intelligence, which specialize in designing and implementing enterprise-level cybersecurity strategies that are both proactive and scalable.
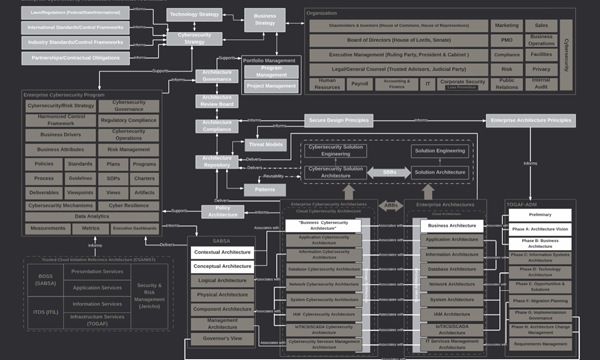
Understanding Enterprise Cyber Security Architecture
At its core, Enterprise Cyber Security Architecture (ECSA) is a structured framework that defines how security technologies, policies, and processes are integrated across an organization’s IT infrastructure. Rather than relying on individual security tools operating independently, the architecture ensures that security mechanisms work together in a layered and coordinated defense model.
Think of it as the security blueprint for an entire organization. Just as architects design buildings with structural integrity and safety in mind, cybersecurity architects design systems that can withstand both current and emerging threats.
A strong enterprise cybersecurity architecture considers the complete digital ecosystem, including:
-
* Corporate networks
-
* Cloud environments
-
* Applications and APIs
-
* Endpoints and user devices
-
* Identity management systems
-
* Data storage and transmission channels
When these elements are protected within a unified framework, organizations gain better visibility, stronger control, and improved resilience against cyber threats.
Why Modern Enterprises Need Cyber Security Architecture
Many organizations initially adopt cybersecurity tools in a reactive manner—deploying firewalls, antivirus software, or monitoring tools as individual solutions to specific problems. While these tools are important, they often operate in silos without a cohesive strategy.
This fragmented approach can create security gaps.
Enterprise Cyber Security Architecture addresses this issue by providing a holistic approach to security, ensuring every component of the digital environment is protected and aligned with business objectives.
Key reasons organizations invest in cybersecurity architecture include:
1. Managing Complex Digital Environments
Modern enterprises operate across hybrid infrastructures involving cloud platforms, on-premise systems, third-party integrations, and remote users. Without a unified architecture, managing security across these environments becomes extremely difficult.
2. Reducing the Attack Surface
A structured architecture helps identify vulnerabilities across the enterprise environment and reduces potential entry points for attackers.
3. Improving Threat Detection and Response
Integrated security systems allow organizations to detect anomalies quickly and respond to incidents before they escalate.
4. Supporting Compliance and Governance
Regulatory frameworks such as ISO 27001, SOC 2, and other industry standards require organizations to implement structured security controls. A well-designed architecture helps align security practices with these compliance requirements.
5. Enabling Secure Digital Transformation
As businesses adopt cloud computing, AI systems, and IoT technologies, cybersecurity architecture ensures that innovation does not compromise security.
Key Layers of Enterprise Cyber Security Architecture
An effective cybersecurity architecture is built on multiple layers of protection. Each layer addresses specific risks within the enterprise ecosystem.
* Network Security
The network is often the first line of defense. Security measures such as firewalls, network segmentation, intrusion detection systems, and secure gateways help monitor and control traffic entering and leaving the organization’s infrastructure.
Network security also includes monitoring internal communications to detect suspicious activity within the environment.
* Identity and Access Management
Identity has become the new security perimeter. With employees accessing systems from multiple locations and devices, organizations must ensure that only authorized users can access sensitive resources.
Identity and Access Management (IAM) solutions implement authentication mechanisms, multi-factor authentication, and role-based access control to prevent unauthorized access.
* Application Security
Applications are among the most targeted components of modern enterprises. Web applications, mobile platforms, and APIs must be tested and secured through practices such as secure coding, vulnerability assessments, and penetration testing.
Proactive testing helps organizations identify vulnerabilities before attackers can exploit them.
* Data Security
Data is one of the most valuable assets for any organization. Enterprise cybersecurity architecture ensures that sensitive information is protected through encryption, data classification, secure storage practices, and controlled access.
Data security also extends to protecting information during transmission and ensuring regulatory compliance for sensitive data.
* Endpoint Security
Every device connected to the network represents a potential entry point for attackers. Endpoint security focuses on protecting laptops, servers, mobile devices, and other endpoints using advanced monitoring and threat detection tools.
With remote work becoming a standard practice, endpoint protection has become increasingly critical.
* Security Monitoring and Incident Response
Security operations centers (SOC) and monitoring systems continuously analyze logs and network activity to detect threats in real time. When suspicious behavior is identified, incident response processes help contain and mitigate the impact of cyber incidents.
The Role of Cybersecurity Consulting in Building Enterprise Security Architecture
Designing and implementing enterprise cybersecurity architecture requires specialized expertise. Organizations must evaluate their current infrastructure, identify potential vulnerabilities, and design a framework that aligns with both business objectives and regulatory requirements.
This is where cybersecurity consulting organizations like Illume Intelligence play a vital role.
Cybersecurity consultants bring a structured approach to security transformation by helping organizations:
-
* Conduct comprehensive security architecture assessments
-
* Identify vulnerabilities through penetration testing and VAPT
-
* Implement risk-based security frameworks
-
* Align cybersecurity practices with global compliance standards
-
* Establish continuous security monitoring and governance models
By combining technical expertise with strategic planning, cybersecurity consultants help organizations move from reactive security to a proactive and resilient security posture.
Enterprise Cybersecurity in the Indian Business Landscape
India’s rapid digital transformation has created immense opportunities for innovation, but it has also increased cyber risks across industries. From manufacturing and healthcare to SaaS platforms and government services, organizations are managing increasingly complex digital infrastructures.
As businesses expand their online presence and adopt cloud technologies, cybersecurity architecture becomes a foundational requirement rather than a technical add-on.
Organizations that adopt enterprise-level cybersecurity frameworks gain several strategic advantages:
-
* Improved operational resilience
-
* Greater trust from customers and partners
-
* Stronger compliance with regulatory requirements
-
* Enhanced protection of intellectual property and sensitive data
Companies that fail to implement structured cybersecurity frameworks often face higher risks of data breaches, operational disruptions, and reputational damage.
Building a Secure and Future-Ready Enterprise
Cybersecurity is no longer limited to protecting systems after deployment. It must be embedded within the very design of enterprise technology environments. Enterprise Cyber Security Architecture provides the structure needed to achieve this goal.
By integrating security across networks, applications, data systems, and operational processes, organizations can create a defense strategy that evolves alongside emerging threats.
Forward-looking organizations are recognizing that cybersecurity architecture is not simply an IT function—it is a business strategy that protects innovation, digital growth, and long-term resilience.
With the support of experienced cybersecurity consulting and compliance organizations such as Illume Intelligence, enterprises can design security frameworks that are scalable, adaptive, and aligned with global best practices.
In an increasingly interconnected digital world, building strong enterprise cybersecurity architecture is not just about preventing attacks. It is about creating a secure foundation that allows businesses to innovate, grow, and operate with confidence.