Designing the business cordial to the Enduser
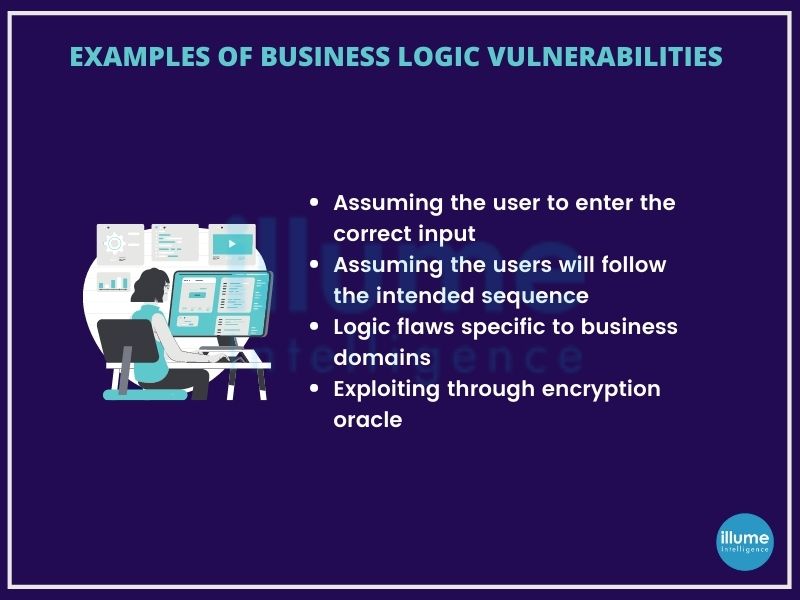
Business logic vulnerabilities are often defined as the flaws in the design and implementation of an application that allows the threat actors to exploit the applications. These flaws generally occur as the developers fail to anticipate the behaviour of the end-user using the application.
Business logic is intended to enforce the rules and constraints defined at the time of designing the application, preventing the users from doing anything that may negatively impact the business. These logic-based vulnerabilities can be extremely diverse depending on the application and its functionalities.
Bugs or flaws in the logic can allow the attackers to outwit these rules. They might exploit by making arbitrary changes in the user data or may pass unexpected values to the server-side of the application forcing it to do unexpected tasks.
The impact of business logic vulnerabilities can be huge. These flaws in logic should be fixed even if the developers can't figure out, how these can be exploited.
Business logic testing or application logic testing, for testing the flaws in a multi-functional application requires unconventional methods. It is not possible to test these vulnerabilities through automated tools, hence it's done by a person.
Why is Business logic testing important for your business?
A logic vulnerability is not a flaw in the coding framework, but the way it is exploited to do something unexpected. developers often focus on making the application user-friendly but are unaware of ways hackers can misuse certain functionalities from the server side as in the case of authorization issues, denial of service etc.
Using both Dynamic Application Security Testing (DAST) and Static Application Security Testing (SAST) the application security can be improved on overall compliance and risk management. Tools included in the manual vulnerabilities finding are OWASP Top 10, CWE Top 25 issues, Cross-Site Scripting (XSS), SQL injection, Fingerprinting, Content Spoofing, Cross-Site Request Forgery (CSRF), URL redirector abuse, Brute Force, etc.
According to the experts, 20% of the vulnerabilities are detected during Business Logic Testing or Application security testing, out of which 80% are of high to medium rating.
Are you looking to remove vulnerabilities of your applications that may lead to serious data breaches? Contact our experts to avail Application logic testing services.