Simulate Real-World Cyberattacks. Validate Your True Security Posture.
Most organizations today rely on vulnerability assessments and compliance audits to measure security.
But attackers don’t follow checklists.
They exploit gaps between tools, teams, and processes — often remaining undetected for weeks.
ILLUME’s Red Team Testing replicates real-world adversaries to identify how far an attacker can penetrate your environment, what they can access, and whether your defenses can actually stop them.

With the increasing size of the organisation, the attack surface also increases and the difficulty to secure and monitor all the endpoints and users. It may be assumed that penetration testing is a great method to secure services, but it often focuses on a specific asset and has a defined scope.
The Reality: Why Red Teaming is No Longer Optional
* Organizations that pass VAPT still suffer breaches
* Advanced attackers mimic legitimate user behavior
* Detection gaps exist across people, processes, and technology
* Compliance frameworks validate controls — not real attack resilience
Red Teaming answers the only question that matters: “If a real attacker targeted your organization today — how far would they get?”
Red Team Testing vs. Penetration Testing
Red Team testing also known as Red Team Security Testing is often confused with penetration testing, but pen testing is only a part of red team assessment. Red team operations have broader objectives than penetration testing.
These assessments are designed to emulate a more real-world scenario, with detailed analysis and defensive strategies. It also includes evasion and persistence, privilege escalation, and exfiltration. The Red team will test the organisation's detection and response capabilities.
How does Illume's Red Team work?
Our Red Team testing methodology covers methods to attempt real-time attacks on an organisation. We follow the ATT&CK Framework, which comprises of the knowledge base of adversary tactics, techniques, and procedures (TTP) based on real red and blue teams’ actual experiences.
The methodology has the following steps -
1. Reconnaissance - This includes Scanning of several areas of the environment to determine interconnecting vulnerabilities and exposure.
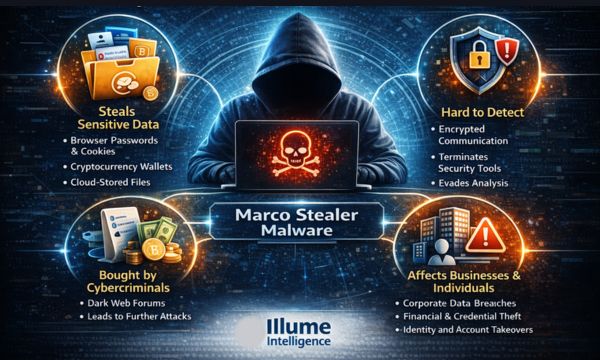
2. Payload & Delivery - It is the ability to deliver a malicious payload of malware, ransomware, and viruses across parts of the environment leveraging email, social media, and web content as a rogue delivery tool.
3. Exploitation - This helps in finding the most susceptible areas to the risks in the environment.
4. Installation - This is to locate the scope of adding rouge devices, including WIFI, servers, and Internet of Things devices, without being detected across several parts of the environment.
5. Command & Control - Locating the endpoints and servers which can receive rouge communication instructions from the hackers.
6. Actions on Objectives - setting objectives to find if the response capabilities and defence mechanisms are working as expected across the environment.
7. Post-Engagement Reporting - The post-engagement report will cover remediation recommendations, including improvements to existing adaptive control and response capabilities, security measures, and incident response protocols.
The Red Team security assessment is a powerful technique for identifying the security vulnerabilities of any organisation. It will expose vulnerabilities, hidden from the organisation and mitigate them. Our Red Team assessment will enhance your organisation's security by uncovering the potential vulnerabilities to level up your security as expected.
What We Offer
Illume delivers objective-driven Red Team engagements tailored to your business, threat landscape, and critical assets.
1. External Red Team Simulation
Simulate attacks originating from outside your organization
* Internet-facing asset exploitation
* Perimeter security testing
* Cloud & web application attack paths
2. Internal Network Compromise Simulation
Assume breach scenarios and test internal resilience
* Lateral movement across systems
* Privilege escalation
* Active Directory exploitation
3. Social Engineering (Optional)
Test human-layer vulnerabilities
* Phishing simulations
* Credential harvesting scenarios
* Insider threat vectors
4. Advanced Adversary Simulation (APT-style)
Mimic sophisticated threat actors
* Stealth-based attack execution
* Persistence techniques
* Evasion of detection mechanisms
5. Business Impact–Driven Reporting
Translate technical findings into business risk
* Attack path visualization
* Risk prioritization
* Executive-level insights
* Remediation roadmap
Take the Next Step
Security controls alone don’t guarantee protection. Validation does.
If your organization is serious about understanding its real security posture:
Schedule a Red Team Strategy Call