Cybercriminals are constantly evolving their tactics, shifting from disruptive attacks to highly profitable data-theft operations. One of the most concerning trends in recent years is the rise of information-stealing malware, commonly referred to as infostealers. These malicious programs are designed not to damage systems immediately but to silently collect valuable data that can later be monetized in underground markets.
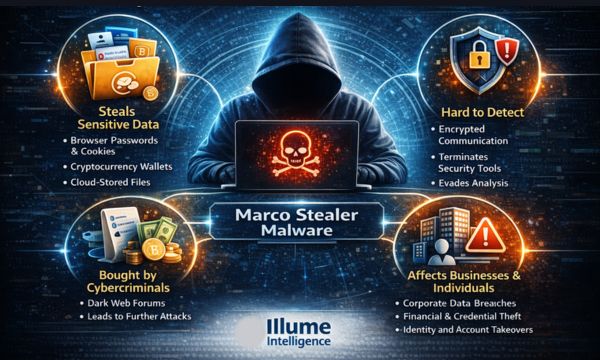
Among the emerging threats in this category, Marco Stealer malware has drawn significant attention from cybersecurity researchers and analysts. Its sophisticated techniques, stealth capabilities, and targeted data-extraction mechanisms make it a particularly dangerous threat to both individuals and enterprises.
Understanding why Marco Stealer is considered dangerous requires examining how it operates, what it targets, and how organizations can defend against such evolving cyber threats.
The Rise of Information-Stealing Malware
Traditional cyberattacks once focused on system disruption—defacing websites, spreading destructive viruses, or shutting down networks. However, modern cybercrime has become more financially motivated. Today’s attackers prioritize data theft, credential harvesting, and identity exploitation because stolen information can easily be sold or used for further attacks.
Infostealer malware has become one of the most widely used tools in cybercriminal operations. These malware variants are designed to collect sensitive information such as:
-
* Login credentials and passwords
-
* Banking and financial data
-
* Cryptocurrency wallet keys
-
* Browser cookies and session tokens
-
* Personal and corporate documents
Once stolen, this data is typically transmitted to remote command-and-control servers, allowing attackers to access accounts, steal funds, or infiltrate corporate networks.
Marco Stealer malware belongs to this new generation of advanced infostealers that operate quietly while extracting large volumes of sensitive information.
What Is Marco Stealer Malware?
Marco Stealer is a credential-harvesting and data-exfiltration malware designed to infiltrate systems and collect sensitive user information without raising suspicion.
Unlike traditional malware that triggers obvious disruptions, Marco Stealer focuses on stealth and persistence. It operates silently in the background, gathering information from various applications and system components before transmitting the data to attackers.
The malware typically spreads through methods such as:
-
* Malicious email attachments
-
* Phishing campaigns
-
* Compromised software downloads
-
* Fake software updates
-
* Malicious browser extensions
Once executed, Marco Stealer begins scanning the infected system for valuable data sources.
What Makes Marco Stealer Malware Dangerous?
Marco Stealer has gained attention in the cybersecurity community because of several advanced capabilities that make it difficult to detect and highly effective for attackers.
Stealth and Evasion Techniques
One of the primary reasons Marco Stealer is considered dangerous is its ability to evade traditional security tools. Many infostealers rely on simple obfuscation techniques, but Marco Stealer employs more sophisticated strategies.
These include:
-
* Encrypted communication with command servers
-
* String obfuscation to hide malicious code behavior
-
* Anti-analysis techniques that terminate security tools
-
* Detection of virtual machines or sandbox environments
These capabilities allow the malware to remain undetected while extracting sensitive information.
Credential and Session Theft
Modern authentication systems often rely on cookies and session tokens to maintain user login sessions. Marco Stealer specifically targets these tokens, allowing attackers to bypass authentication without needing the original password.
By stealing browser session data, attackers can gain direct access to:
-
* Email accounts
-
* Cloud services
-
* Enterprise dashboards
-
* Social media platforms
-
* Online banking portals
This form of credential abuse is particularly dangerous because victims may not immediately notice that their accounts have been compromised.
Cryptocurrency Wallet Targeting
Cryptocurrency users are another major target of Marco Stealer malware. The malware scans browser extensions and local files for wallet information associated with popular crypto platforms.
If wallet credentials or private keys are discovered, attackers can quickly transfer funds to anonymous wallets, making recovery nearly impossible.
As cryptocurrency adoption continues to grow globally, this capability makes Marco Stealer especially lucrative for cybercriminal groups.
Cloud Data Exfiltration
Another concerning capability of Marco Stealer is its ability to access data stored in cloud-synchronized folders. Many users automatically sync documents with platforms such as Google Drive, OneDrive, or Dropbox.
If a compromised system has access to these folders, the malware may extract:
-
* Corporate documents
-
* Financial spreadsheets
-
* Client records
-
* Confidential internal communications
For organizations, this creates a significant risk of data breaches and intellectual property theft.
Silent Persistence
Marco Stealer is designed to operate quietly without causing system instability or noticeable performance issues. Because it avoids disruptive behavior, infections can remain active for extended periods.
During this time, attackers may continuously harvest new credentials and sensitive information as users interact with their systems.
This persistence significantly increases the damage potential of the malware.
Why Businesses Should Be Concerned
Although many infostealer infections initially target individuals, the stolen data often becomes a gateway into corporate networks. For example, compromised employee credentials can be used to access enterprise systems or cloud platforms.
This can lead to:
-
* Unauthorized access to internal systems
-
* Corporate data breaches
-
* Financial fraud
-
* Supply chain attacks
-
* Ransomware deployment within enterprise networks
In many cases, infostealer malware acts as the first stage of larger cyberattacks.
Organizations that rely heavily on remote work, cloud platforms, and digital collaboration tools must therefore treat infostealer threats as a serious cybersecurity risk.
Preventing Marco Stealer Infections
While Marco Stealer malware poses significant risks, organizations can take several proactive steps to reduce their exposure.
Strengthening Endpoint Security
Advanced endpoint detection and response (EDR) systems can identify suspicious behavior associated with malware infections.
These tools analyze system activity patterns rather than relying solely on known malware signatures.
Implementing Multi-Factor Authentication
Multi-factor authentication (MFA) adds an additional security layer that reduces the impact of stolen passwords. Even if credentials are compromised, attackers may still be blocked without the second authentication factor.
Conducting Security Awareness Training
Many malware infections begin with phishing attacks. Training employees to identify suspicious emails, links, and downloads can significantly reduce infection rates.
Regular Vulnerability Assessments
Routine vulnerability assessments help identify security weaknesses that attackers might exploit. Penetration testing can further validate the effectiveness of security controls.
The Role of Cybersecurity Consulting in Threat Mitigation
Defending against sophisticated malware threats requires a combination of technology, strategy, and continuous monitoring. Organizations often need specialized expertise to design effective cybersecurity programs.
Cybersecurity consulting firms such as Illume Intelligence assist enterprises in evaluating their security posture and implementing proactive defense strategies.
Through services like vulnerability assessments, penetration testing, threat monitoring, and compliance consulting, organizations can build stronger defenses against emerging cyber threats such as Marco Stealer.
The goal is not only to detect threats but also to create resilient security architectures capable of adapting to evolving attack techniques.
Staying Ahead of Emerging Cyber Threats
The emergence of Marco Stealer highlights a broader shift in cybercrime strategies. Attackers are increasingly focusing on stealthy data theft rather than immediate disruption.
This trend makes early detection and proactive cybersecurity measures more important than ever.
Organizations must recognize that modern cyber threats are intelligent, persistent, and financially motivated. Protecting digital assets requires continuous monitoring, advanced security technologies, and a strong cybersecurity culture.
By adopting proactive security strategies and working with experienced cybersecurity professionals, businesses can significantly reduce the risk posed by advanced malware threats such as Marco Stealer.